Digital transformation is reshaping manufacturing. Smart factories, connected machinery, and

Remote work has become the norm across enterprises, but traditional
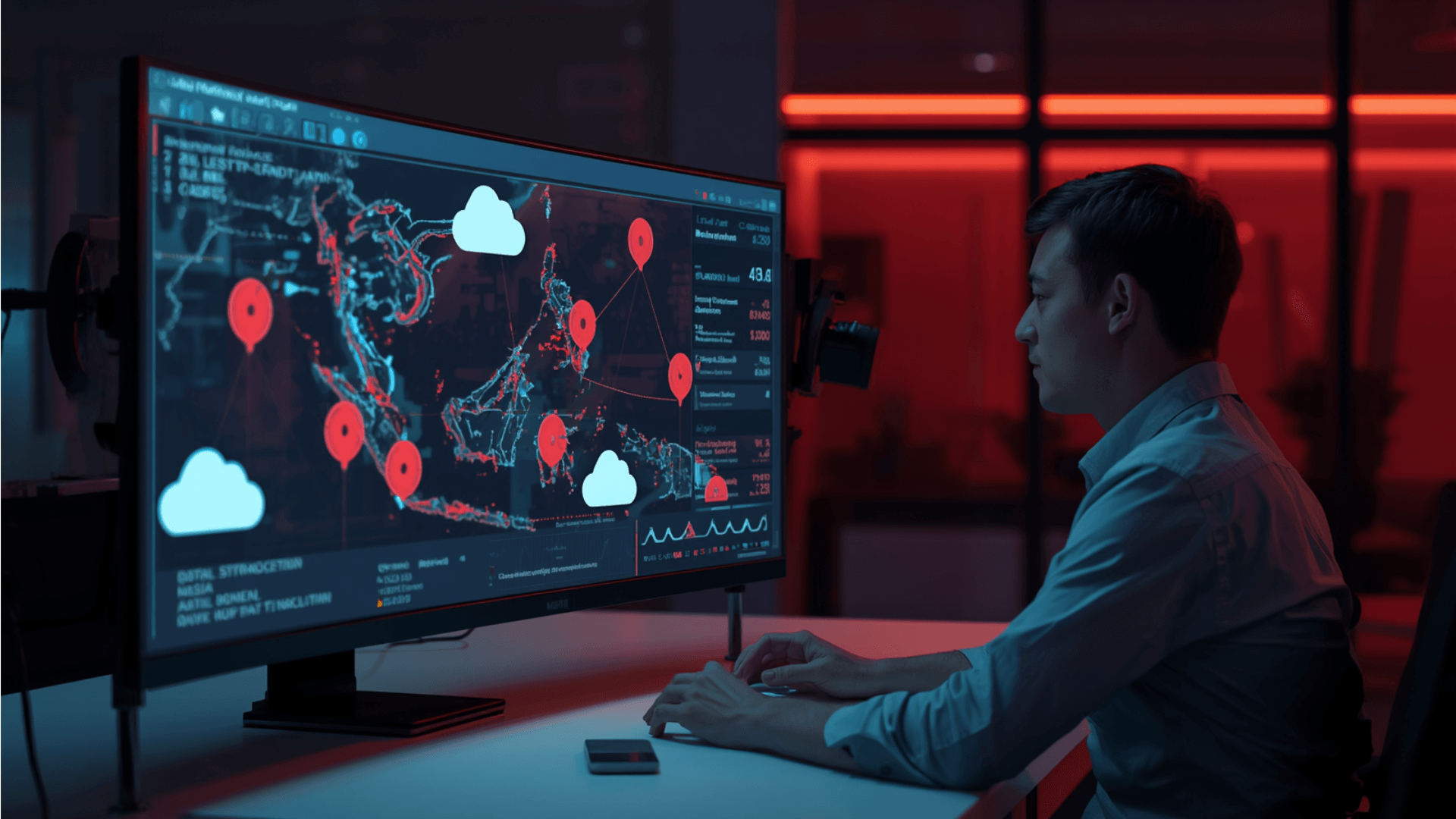
As the landscape of cyber threat intelligence in Asia evolves,
As organisations increasingly adopt Kubernetes and containerised applications, DevSecOps teams
Underground forums, dark web marketplaces, and encrypted chat channels generate
Cybersecurity leaders are being asked to strengthen protection while spending