As the landscape of cyber threat intelligence in Asia evolves, state-sponsored advanced persistent threats (APTs) pose a growing risk to regional enterprises. These attacks are typically highly targeted, well-resourced, and designed to remain undetected for extended periods. Unlike opportunistic cybercrime, APTs aim for strategic objectives such as intellectual property theft, critical infrastructure disruption, or geopolitical advantage.
Asian organisations, particularly in sectors like finance, telecommunications, energy, and critical infrastructure security, face increasing exposure due to rapid digitalisation and high-value data assets. Defending against these threats requires a proactive, intelligence-driven approach that combines technical controls, human expertise, and continuous monitoring.
Why APTs Are a Unique Threat
APTs differ from regular cyberattacks in several key ways:
- Long-term persistence: Attackers infiltrate systems quietly, often remaining undetected for months or even years.
- Highly targeted operations: They focus on high-value assets rather than broad attacks.
- Custom tools and malware: Instead of relying solely on known exploits, APT groups develop bespoke malware and sophisticated adversarial tactics.
- Multi-stage campaigns: APT attacks often involve reconnaissance, initial access, lateral movement, privilege escalation, and exfiltration in carefully coordinated phases.
According to the 2023 Verizon Data Breach Investigations Report, 71% of organisations experienced at least one advanced persistent threat intrusion in the past year, highlighting the widespread and persistent danger posed by state-sponsored groups. To counter this, leveraging cyber threat intelligence in Asia is essential for identifying regional-specific attack patterns.
Key Steps for Defending Against APTs
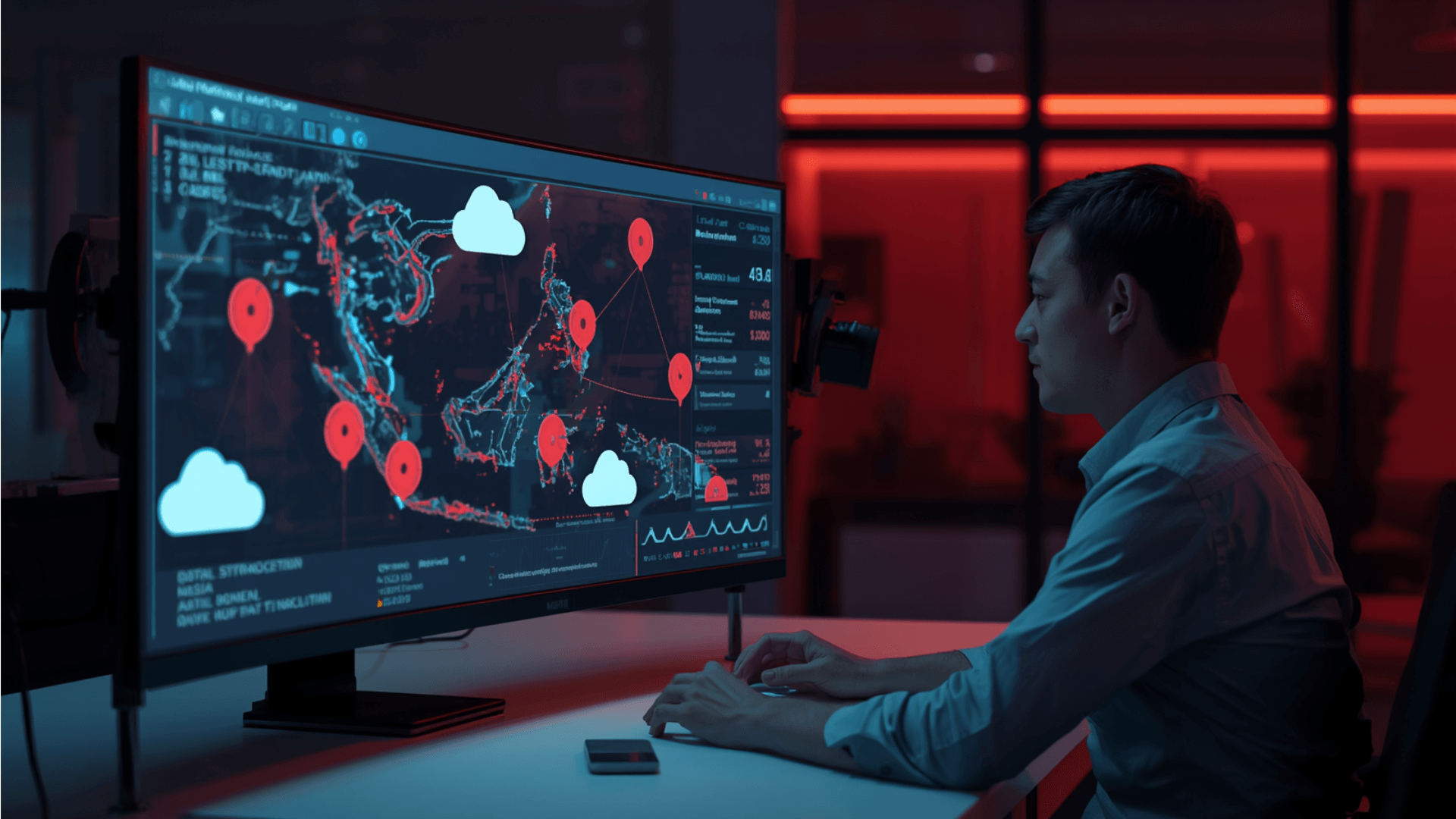
- Intelligence-driven threat hunting: Integrating threat intelligence feeds allows organisations to identify indicators of compromise (IOCs) and attacker tactics, techniques, and procedures (TTPs). Proactively hunting for anomalies based on cyber threat intelligence in Asia helps detect advanced threats early, reducing dwell time.
- Network segmentation and least privilege: Isolating critical systems restricts lateral movement within the network. By limiting access rights, organisations reduce the exposure of sensitive data.
- Continuous monitoring and detection: Monitoring across endpoints, servers, and cloud services enables organisations to spot unusual behaviours. Advanced behavioural analytics help identify threats that evade traditional signature-based defences.
- Vulnerability management: Regularly scanning and patching systems is essential for effective advanced persistent threat protection. Prioritising vulnerabilities that allow initial access or privilege escalation ensures critical weaknesses are addressed promptly.
- Incident response preparedness: Developing and testing response plans tailored to APT scenarios ensures teams can respond efficiently.
- Supply chain security: Auditing vendors prevents attackers from exploiting third-party relationships. Verifying the integrity of software and hardware strengthens the overall security posture.
Building a Resilient Cybersecurity Posture
Defending against state-sponsored APTs requires more than tools; it demands a holistic approach combining technology, processes, and people. Organisations must foster a security-aware culture and integrate proactive threat hunting with decisions driven by cyber threat intelligence in Asia. Investing in these capabilities helps Asian enterprises identify advanced threats early and maintain operational continuity.
Strengthening Your Defence Against APTs
State-sponsored APTs are persistent, adaptive, and highly skilled. Asian enterprises that proactively implement intelligence-led threat detection, robust network controls, and rigorous incident response planning will be better equipped to defend critical assets.
Partner with Zentara to integrate the latest cyber threat intelligence in Asia into your security operations. Strengthen your defence against APTs and safeguard sensitive information against evolving state-sponsored threats.