Digital transformation is reshaping manufacturing. Smart factories, connected machinery, and Industrial IoT are improving efficiency and productivity. However, this convergence of Information Technology (IT) and Operational Technology (OT) has also created new cybersecurity challenges. Historically, these environments were managed separately, with different priorities and cultures.
Today, attackers actively exploit the gaps between these teams. Establishing a baseline for IT-OT convergence security is no longer optional; it is essential for protecting modern manufacturing operations.
Why the IT–OT Gap Exists
Understanding the root causes of the divide is the first step toward fixing it. IT teams typically focus on data confidentiality and integrity, while OT teams prioritise safety and uptime. Security controls that seem routine in IT can disrupt production in OT environments.
Furthermore, legacy Industrial Control Systems (ICS) security often suffers because these systems were designed decades ago without cybersecurity in mind. They frequently rely on proprietary protocols and equipment that cannot be easily patched. This separation of tools and visibility creates blind spots that undermine IT-OT convergence security across the enterprise.
Why Bridging the Gap Matters
The convergence of IT and OT has significantly increased the cyber risk facing manufacturing organisations. Attackers understand that operational pressure in manufacturing increases the likelihood of rapid ransomware payment. Unlike traditional IT breaches, incidents in cyber-physical systems can have real-world impact, including equipment damage or safety risks for employees.
Ultimately, improving IT-OT convergence security impacts overall operational technology resilience. Governments are strengthening requirements for critical infrastructure, meaning manufacturers must demonstrate risk management across both environments.
Common Security Challenges in IT–OT Environments
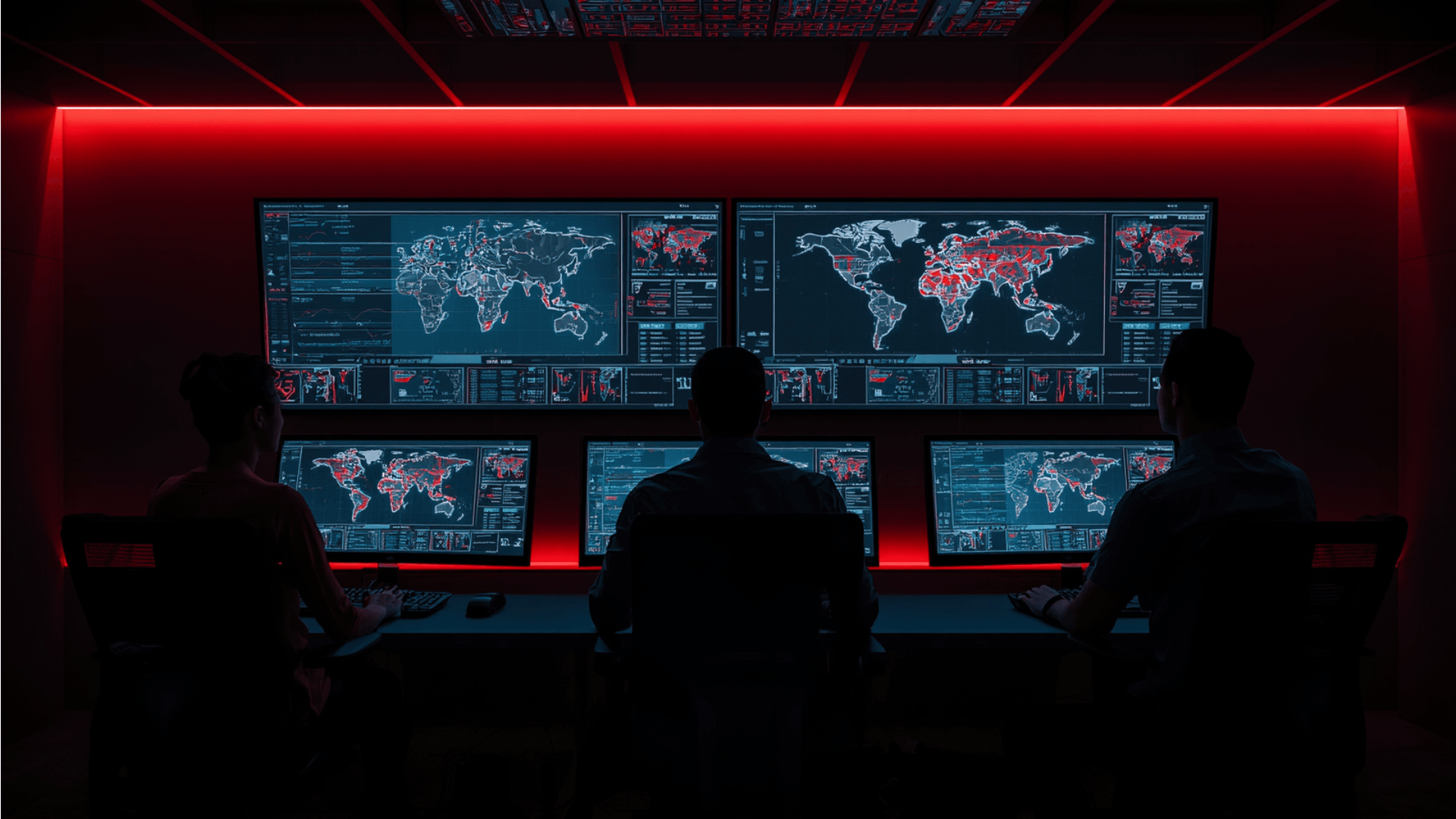
As IT and OT environments converge, manufacturers face several recurring security challenges that increase exposure to cyber threats.
- Limited asset visibility: Many organisations lack a complete inventory of connected industrial devices. Shadow assets and unmanaged systems create hidden entry points and slow down incident response.
- Weak network segmentation: Flat or poorly segmented networks allow attackers to move from corporate IT into production environments. Once inside OT networks, intrusions can remain undetected for long periods.
- Inconsistent patch and vulnerability management: Patching OT systems requires careful coordination to avoid downtime. As a result, known vulnerabilities often remain unaddressed longer than in IT environments.
- Third-party and remote access risks: Vendors frequently require remote access to maintain equipment. Without strong access controls and monitoring, compromised credentials can provide privileged entry into critical systems.
Strategies to Align IT and OT Security Teams
Bridging the IT–OT divide requires a coordinated approach that combines governance, technology, and collaboration.
1. Establish shared governance and leadership
Create a unified security governance model that includes IT, OT, risk, and operations leaders. Define shared ownership of cyber risk, clear escalation paths, and joint decision-making processes. This prevents gaps in responsibility and ensures security priorities align with operational goals.
2. Develop a unified risk framework
Adopt a risk model that evaluates both cyber impact and operational consequences such as downtime, safety, and production loss. This helps teams prioritise investments and security controls based on real business risk rather than technical severity alone.
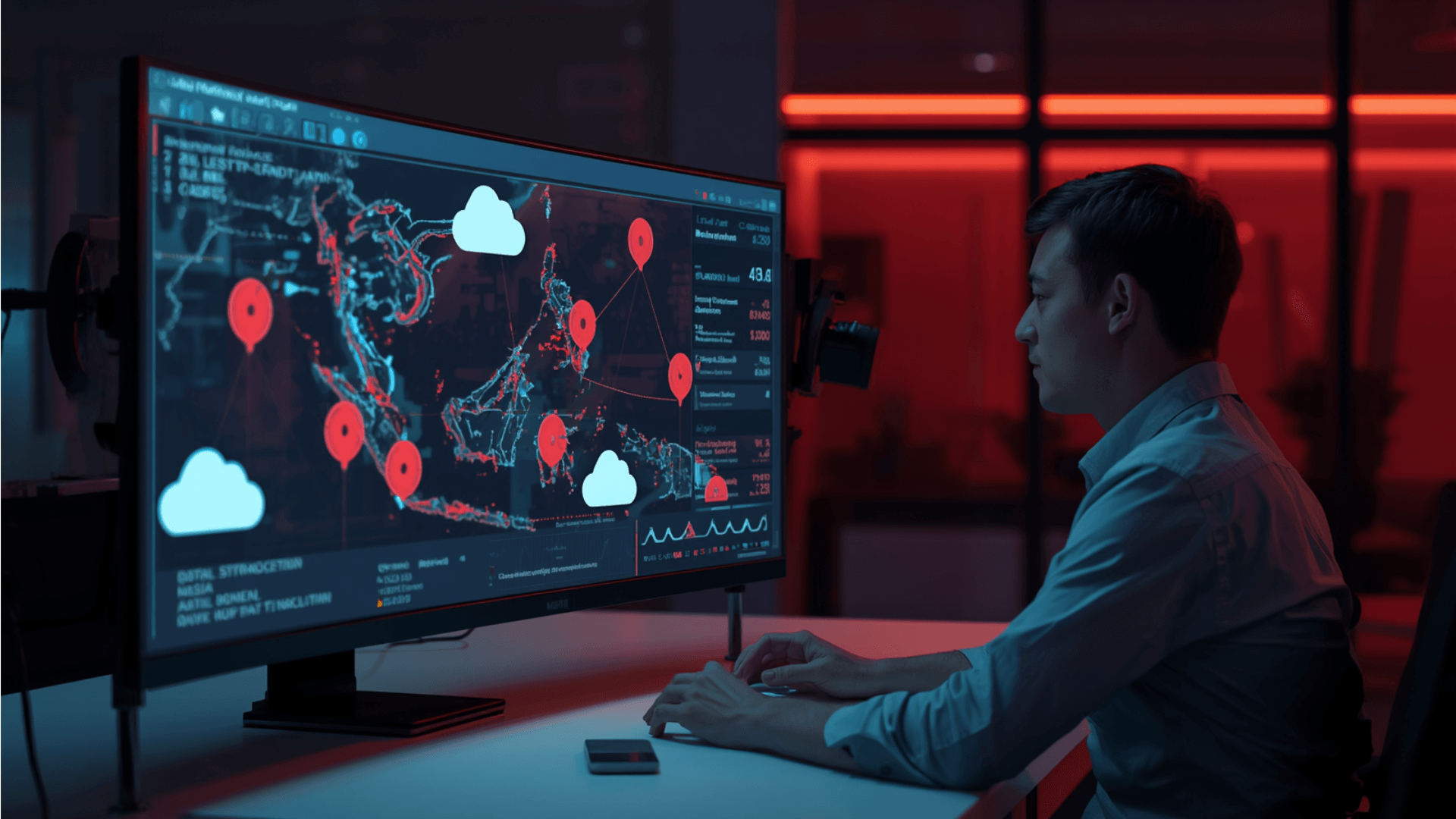
3. Improve asset discovery and visibility
Deploy tools that can automatically discover and monitor assets across both IT and OT networks without disrupting operations. A complete asset inventory enables better vulnerability management, faster incident response, and improved compliance reporting.
4. Implement strong network segmentation
Segment corporate IT and critical control systems using firewalls and zero-trust principles. Proper segmentation limits lateral movement and strengthens IT-OT convergence security.
5. Align incident response processes
Develop incident response plans that include both cybersecurity and operational scenarios. Conduct joint tabletop exercises and simulations so IT and OT teams can practise coordination, communication, and recovery procedures.
6. Strengthen identity and access management
Apply least-privilege access, multi-factor authentication, and secure remote access for employees, contractors, and vendors. Identity-based security is essential to prevent unauthorised access to sensitive industrial systems.
Building a Unified IT–OT Security Culture
Technology and processes are essential, but lasting progress depends on collaboration and shared ownership of cyber risk. Manufacturing organisations that foster a unified security culture are better positioned to protect production environments while maintaining operational efficiency.
Encourage cross-team learning and knowledge sharing
IT teams must understand operational constraints such as safety, uptime, and change management, while OT teams need stronger cybersecurity awareness. Regular workshops, joint exercises, and shared documentation help both sides make informed decisions and reduce friction during incidents.
Define shared metrics and success criteria
Security performance should reflect both cyber resilience and operational continuity. Establishing shared KPIs such as incident response time, asset visibility coverage, and downtime reduction encourages collaboration rather than competing priorities.
Secure executive sponsorship
Leadership plays a critical role in breaking down organisational silos. Executive backing ensures consistent funding, clear accountability, and long-term commitment to integrated IT–OT security initiatives.
Advancing Cyber Resilience in Smart Manufacturing
As manufacturing environments become more connected, the distinction between IT and OT continues to fade. Organisations that align teams and technology gain stronger visibility and improved business continuity. Securing the future of IT-OT convergence security is no longer optional; it is a strategic priority for smart manufacturing.
Organisations seeking to accelerate maturity can explore the Zentara Cyber Intelligence Platform to support a unified security strategy across industrial environments.