Security teams are not short on tools. They are short on clarity. SIEM, SOAR, and XDR are often discussed as interchangeable or as successive “upgrades” to one another. In reality, they solve different problems, operate at different layers, and fail for different reasons when misused. Understanding XDR vs SIEM vs SOAR is less about product categories and more about how detection, response, and decision-making actually work in modern security operations.
Why XDR vs SIEM vs SOAR Gets Confusing
The confusion usually comes from overlapping marketing claims. Vendors promise faster detection, automated response, and reduced analyst workload. What they often do not explain clearly is where responsibility still sits with humans and where automation should stop. According to IBM’s Cost of a Data Breach Report 2025, organizations using extensive security automation saved an average of USD 1.76 million per breach, but only when automation was properly integrated into workflows and governance models. Tools alone do not create those savings. Architecture and operating discipline do.
What SIEM Does (and What it Doesn’t)
Security Information and Event Management Explained
Security information and event management (SIEM) platforms centralize log data from across the environment. Their core value is visibility.
SIEM platforms:
- Collect and normalize logs from endpoints, servers, cloud services, and network devices
- Correlate events over time
- Support compliance reporting and forensic investigation
Gartner describes SIEM as foundational for detection and investigation, not response automation
Where Teams Misuse SIEM
The most common failure is treating SIEM as a detection engine instead of a data layer.
SIEM alerts are only as good as:
- Log coverage
- Detection rules
- Ongoing tuning
Without dedicated ownership, SIEM becomes noisy, expensive, and underused. Many teams forward alerts into ticketing systems without context, creating analyst fatigue instead of clarity.
What SOAR Does (and Where it Breaks)
Security Orchestration, Automation, and Response in Practice
Security orchestration, automation, and response (SOAR) focuses on execution.
SOAR platforms:
- Automate repetitive response tasks
- Orchestrate actions across tools
- Enforce playbooks for common incidents
According to Palo Alto Networks Unit 42, SOAR can reduce incident response time by up to 80% when playbooks are well defined.
SOAR vs SIEM: The Common Misalignment
The SIEM vs SOAR distinction is simple but often ignored.
SIEM answers: What happened?
SOAR answers: What should we do next?
Teams misuse SOAR when they:
- Automate decisions instead of actions
- Encode flawed or outdated playbooks
- Deploy automation without governance
Automation amplifies whatever logic you give it, good or bad.
What XDR Changes (and What It Doesn’t Replace)
Extended Detection and Response Defined
Extended detection and response (XDR) unifies detection and investigation across multiple security layers.
XDR platforms:
- Correlate telemetry across endpoint, network, identity, cloud, and email
- Apply analytics to surface higher-confidence detections
- Reduce tool sprawl by consolidating signals
According to Microsoft, XDR improves detection accuracy by correlating signals across multiple domains rather than analysing alerts in isolation, helping security teams reduce noise and prioritise incidents that represent real risk. Microsoft emphasises that XDR is designed to augment analyst decision-making, not replace existing security operations tools or human judgment, especially in complex enterprise environments.
XDR vs SIEM vs SOAR in Real Operations
XDR does not replace SIEM or SOAR outright.
- SIEM remains essential for compliance, long-term retention, and custom log sources
- SOAR remains critical for structured response and enforcement
- XDR improves detection quality and investigation speed
Problems arise when XDR is treated as a “single pane of glass” that eliminates the need for operational discipline.
How Security Teams Actually Get Value
High-performing SOCs follow a clear division of responsibility:
- SIEM for visibility, correlation, and compliance
- XDR for high-fidelity detection and investigation
- SOAR for controlled, governed response
NIST’s Cybersecurity Framework emphasizes that detection and response must remain accountable processes, not just automated workflows The tools support decisions. They do not own them.
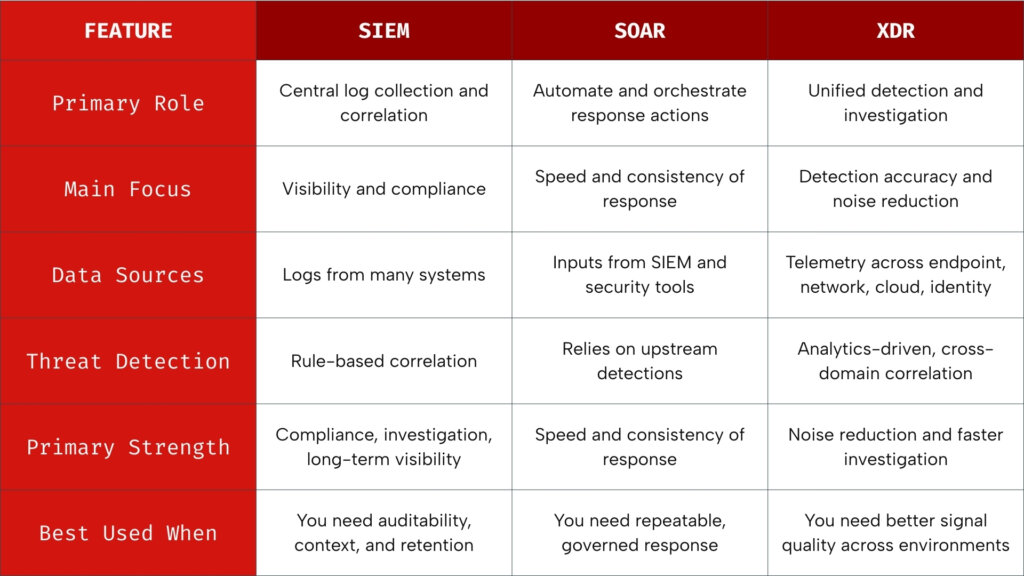
SIEM provides context. XDR sharpens signals. SOAR executes intent. Value comes from architecture, not tool replacement.
XDR vs SIEM vs SOAR: Choosing Architecture, Not Tools
Teams fail when they ask, “Which tool should we buy?”
The better question is, “Where does detection end and decision-making begin?”
Used correctly:
- SIEM provides context
- XDR sharpens signals
- SOAR executes intent
Used incorrectly, they create false confidence, fragmented visibility, and hidden risk.
Security maturity is not about stacking tools. It is about designing workflows where automation accelerates humans instead of replacing judgment.
This is where execution matters. At Zentara, we work with organisations to design SOC models where XDR, SIEM, and SOAR are applied deliberately, not piled on reactively. Whether through SOC-as-a-Service, fully managed SOC operations, or hybrid SOC environments, the focus stays the same: clear visibility, disciplined response, and automation that supports analysts instead of obscuring risk. The result is security operations that scale with the business without sacrificing accountability or control.