Modern enterprises don’t operate in isolation. Cloud providers, SaaS platforms, payment processors, development partners, logistics vendors—every business today runs on an extended ecosystem of third parties. Each one expands capability. Each one also expands risk.
High-profile breaches over the last few years have made one thing clear: attackers no longer need to break your defenses if they can compromise someone you trust. This is why third-party risk assessments have moved from a compliance checkbox to a core security requirement.
Why Third-Party Risk Keeps Failing in Practice
Most organizations think they manage vendor risk. In reality, many rely on surface-level questionnaires, annual reviews, or contractual assurances that don’t reflect real-world exposure.
This gap has been repeatedly exposed in real-world incidents.
A widely cited example is the Target breach, where attackers gained access through a third-party HVAC vendor with network credentials that were far broader than necessary. The issue was not a lack of security tools, but insufficient control over vendor access and monitoring
More recently, the SolarWinds supply chain compromise demonstrated how trusted software vendors can become large-scale attack vectors when third-party software updates are implicitly trusted without continuous validation
In 2023, Okta disclosed a breach originating from its customer support system, where attackers accessed session tokens through a third-party environment, impacting multiple downstream customers. The breach highlighted weaknesses in vendor access governance and post-assessment enforcement
Common failure points include:
- One-time assessments that don’t reflect ongoing changes in vendor environments
- Generic questionnaires that vendors can easily “pass” without evidence
- Lack of technical validation of controls
- No ownership once a risk is identified
- No enforcement mechanisms when vendors fail to improve
Attackers understand this gap. Vendors are often less mature, less monitored, and more permissive than the enterprises they serve. That makes them ideal entry points.
What a Real Third-Party Risk Assessment Actually Evaluates
An effective risk assessment for third parties goes beyond policy review. It evaluates how vendor weaknesses could translate into direct impact on your organization.
At a minimum, mature assessments examine:
1. Access pathways
What systems does the vendor access? Are integrations limited by least privilege, or are credentials shared broadly? Many breaches escalate simply because vendor access was never constrained.
2. Data exposure
What data is shared, processed, or stored by the vendor? Is sensitive or regulated data involved? Is data encrypted at rest and in transit? Are retention and deletion policies enforced?
3. Security control maturity
Does the vendor actually operate security controls, or do they only document them? This includes patch management, logging, monitoring, backup integrity, and incident response readiness.
4. Incident response alignment
If the vendor is breached, how—and how quickly—will you know? Are notification timelines contractually defined? Are incident response roles and escalation paths clear?
5. Regulatory and compliance alignment
Does the vendor’s security posture align with applicable requirements such as PDPD (Indonesia), PDPA, GDPR, or sector-specific standards? Misalignment here often creates downstream legal exposure.
Why Questionnaires Alone Are Not Enough
Questionnaires are useful, but only as a starting point. They are self-reported, static, and rarely validated. Vendors know how to answer them.
Without verification, organizations end up with:
- False confidence in vendor security posture
- Risk registers full of unprioritized findings
- No clarity on which vendors pose existential risk versus tolerable risk
Effective third-party risk assessments combine governance review with technical validation.
This may include evidence requests, architecture reviews, targeted security testing, and continuous monitoring for high-risk vendors.
Prioritizing Vendors By Real Business Impact
Not all vendors deserve the same level of scrutiny. Mature programs tier vendors based on business criticality and exposure, not vendor size or brand reputation.
A practical approach:
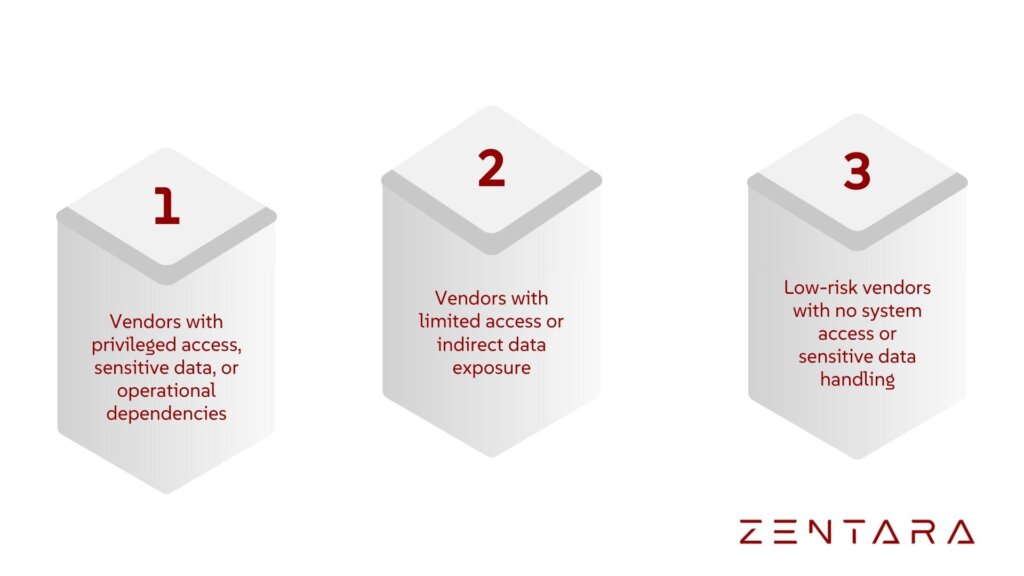
Deep, recurring assessments should focus on Tier 1 vendors. Everything else becomes noise.
Closing the Loop: Assessment Without Enforcement Is Theater
One of the most common failures in third-party risk programs is what happens after risks are identified.
A credible program defines:
- Clear remediation expectations
- Timelines tied to risk severity
- Consequences for non-compliance
- Executive ownership when exceptions are accepted
Security findings that don’t change behavior don’t reduce risk.
Making Third-Party Risk a Living System
Threats change. Vendors evolve. Mergers happen. Cloud architectures shift. A third-party risk assessment performed once a year cannot keep up with this reality.
High-maturity organizations treat vendor risk as a living system, supported by:
- Continuous reassessment for critical vendors
- Integration with SOC and incident response workflows
- Intelligence-led monitoring for emerging vendor-related threats
- Clear alignment between security, procurement, and legal teams
This approach turns third-party risk from a defensive exercise into an operational advantage.
Why Enterprise Risk Assessment Matters in 2026
As enterprises accelerate digital transformation, vendor ecosystems will only grow more complex. Attackers are already exploiting that complexity.
Organizations that fail to operationalize third-party risk assessments will continue to discover weaknesses only after incidents occur, when options are limited and impact is unavoidable.
Stopping vendors from becoming your weakest link starts with treating risk assessment as a real security function, not a compliance formality.
Ready to secure your business? Contact Zentara today and request an enterprise risk assessment or explore our services to find the solution you need.as AI adoption accelerates.