Every enterprise today is digital at its core. From e-commerce to financial services, healthcare to manufacturing, businesses depend on connected systems, cloud environments, and data-driven operations to thrive. But as technology scales, so do risks—creating the need for advanced cybersecurity services that go beyond basic protection.
The stakes are enormous. According to IBM’s 2024 Cost of a Data Breach Report, the global average cost of a data breach reached $4.45 million—the highest ever recorded. Beyond financial damage, breaches erode customer trust, disrupt operations, and in regulated industries, trigger severe compliance penalties.
The natural response has been to invest more in cybersecurity tools and talent. Yet many organizations still struggle. Cybersecurity talent is scarce, sophisticated threats bypass traditional defenses, and running an in-house Security Operations Center (SOC) requires significant resources.
This is why enterprises are increasingly turning to SOC as a Service, a modern, scalable, and effective approach to securing their digital future.
What is SOC as a Service?
SOC as a Service delivers the functionality of a traditional Security Operations Center, continuous monitoring, threat detection, incident response, and compliance support through a managed, outsourced model.
Instead of building and maintaining an in-house SOC with costly infrastructure and staff, businesses partner with a trusted cybersecurity company that provides these services remotely.
Core Functions of SOC as a Service:
- 24/7 Monitoring and Alerting: Continuous observation of network activity, endpoints, cloud services, and applications, providing essential protection for modern cloud security.
- Threat Detection and Analysis: Using advanced analytics, machine learning, and global cyber threat intelligence to identify and prioritize risks.
- Incident Response: Rapid containment, eradication, and recovery when attacks occur.
- Proactive Threat Hunting: Human-led investigations to uncover hidden or advanced persistent threats.
- Compliance Reporting: Logging, monitoring, and reporting tailored to industry regulations.
This approach ensures enterprises receive enterprise-grade protection without the prohibitive costs of building their own facility.
How SOC as a Service Works
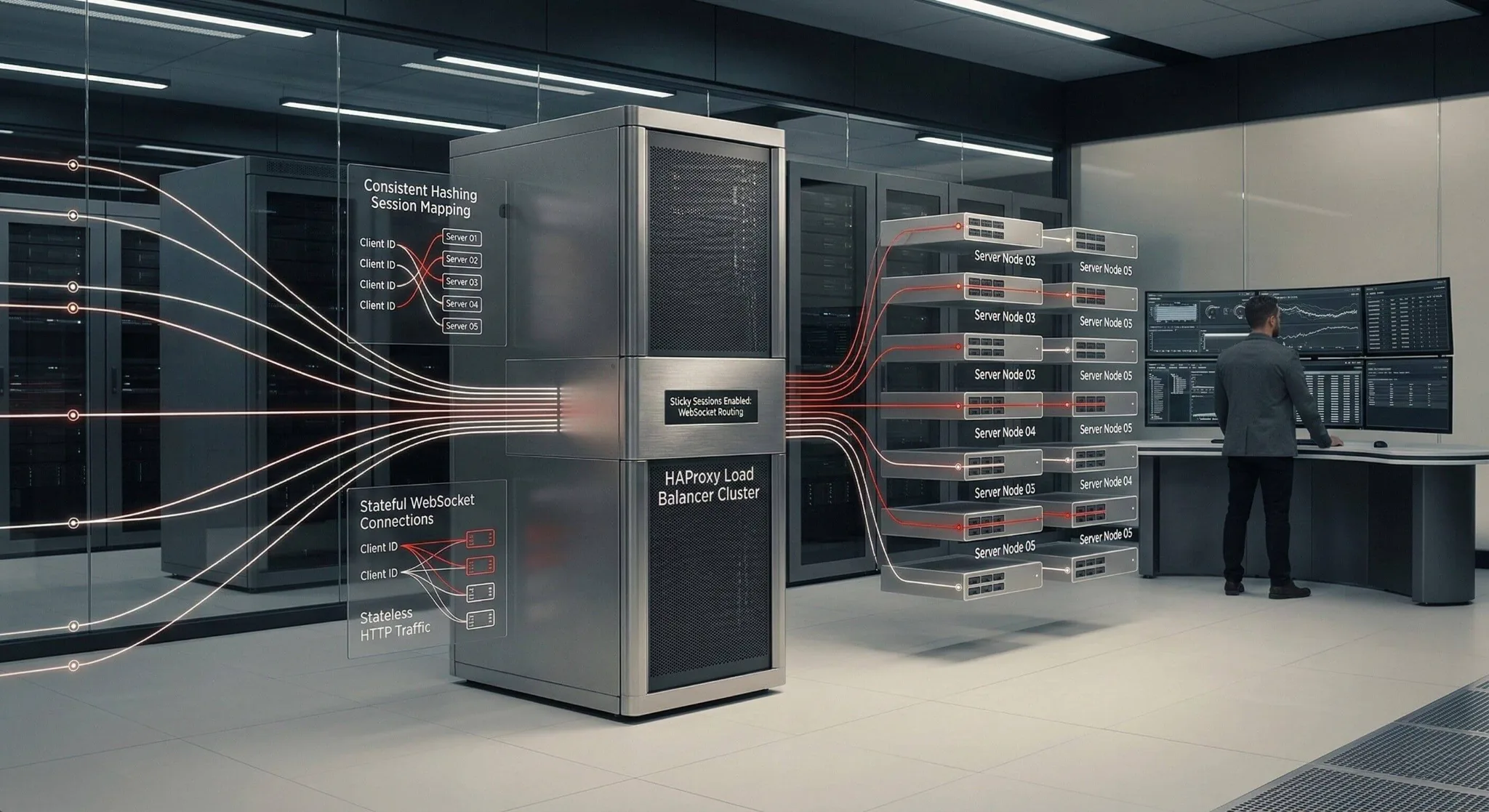
At its heart, SOC as a Service combines three critical elements: technology, people, and process.
- Technology Stack
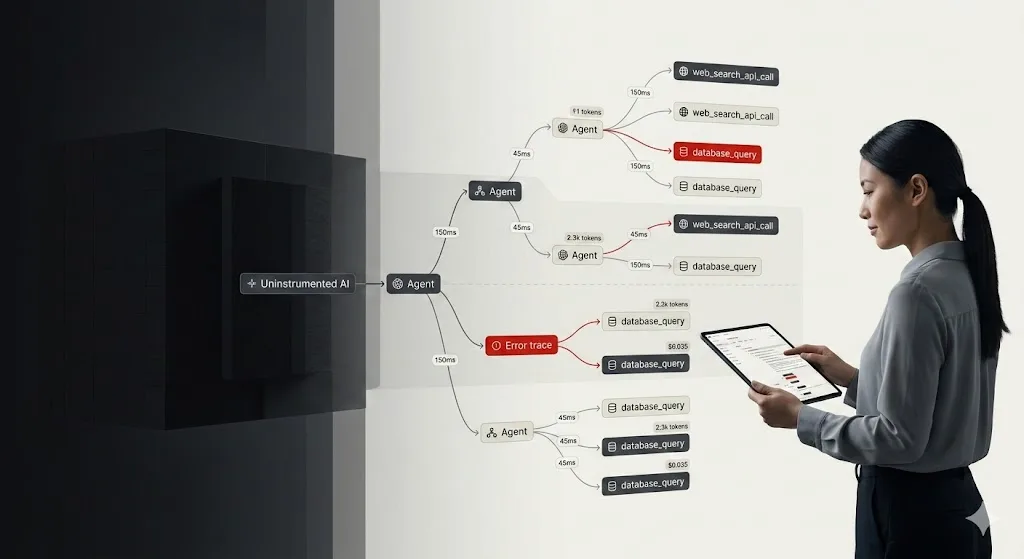
Security Information and Event Management (SIEM) platforms collect and correlate logs across endpoints, cloud environments, and applications. Security Orchestration, Automation, and Response (SOAR) tools automate response workflows. Machine learning and AI-driven analytics enhance detection accuracy and reduce false positives. - Expert Analysts
A SOC is only as effective as the people behind it. Certified analysts monitor dashboards, validate alerts, and respond to incidents. Their expertise enables them to separate real threats from noise and guide businesses through containment and remediation. - Structured Processes
From onboarding to continuous optimization, SOC as a Service follows standardized playbooks for detection, escalation, incident response, and reporting. This ensures consistency, speed, and compliance.
Why Businesses Need SOC as a Service
The demand for SOC as a Service is being driven by three fundamental challenges:
- Escalating Threat Landscape
Cyberattacks are more sophisticated than ever. According to Secureframe, the average time to detect a breach is 204 days, with another 73 days required to contain it. That’s nearly nine months of potential damage. - Skills Shortage
Cybersecurity talent is scarce worldwide. Building an in-house SOC requires hiring and retaining experts—something that even large enterprises find difficult. SOC as a Service bridges this skills gap. - Cost and Complexity
Standing up a full SOC involves millions in technology investments, ongoing staff salaries, training, and 24/7 operations. SOC as a Service eliminates these costs while delivering the same—if not superior—capabilities.
The Tangible Benefits of SOC as a Service
For enterprises, SOC as a Service delivers measurable advantages:
- Reduced Risk of Breach: Continuous monitoring and proactive defense reduce the likelihood of successful attacks.
- Faster Incident Response: Minimize downtime and costs by accelerating detection and containment.
- Compliance Assurance: Meet obligations under standards like ISO 27001, PCI DSS, and Indonesia’s Personal Data Protection Act.
- Optimized Spending: Access enterprise-grade protection without the expense of in-house infrastructure.
- Unified Visibility: Centralized view of security posture across all digital assets.
- Peace of Mind: Knowing that experts are watching over your systems 24/7.
Zentara’s Approach: Why Choose Us for SOC as a Service
While many vendors provide generic IT services, we focus exclusively on cybersecurity services that combine global expertise with local insights.
Key Differentiators:
- 24/7 Global Coverage: Our analysts work around the clock to ensure constant protection.
- Certified Experts: Our team includes specialists with SANS, OSCP, and CISSP certifications.
- Cutting-Edge Technology: Integration of SIEM, SOAR, EDR, AI-driven analytics, and cyber threat intelligence for stronger detection and response.
- Proactive Threat Hunting: We don’t wait for alerts—we seek out adversaries before they strike.
- Compliance Focused: Designed to align with global standards and local regulations.
- Scalable and Flexible: Our service adapts as your business and threats evolve.
This unique blend of features makes Zentara more than just another cybersecurity company—we are your trusted security partner.
Case for Growth: Market Validation
The market momentum is undeniable. According to MarketsandMarkets, the global SOC as a Service market was valued at USD 7.37 billion in 2024 and is projected to reach USD 14.66 billion by 2030, growing at a CAGR of 12.2 percent.
Enterprises are clearly recognizing that SOC as a Service is no longer optional—it’s essential.
The Risk of Fragmentation
Organizations often struggle with fragmented security tools. TechRadar reports that companies dealing with tool sprawl take 72 days longer to detect threats and 84 days longer to contain them. This highlights the need for a unified, streamlined approach—precisely what Zentara’s Managed SOC delivers.
Future Outlook: The Evolution of SOC as a Service
As technology advances, SOC as a Service will evolve in three key directions:
- AI-Driven Security: Greater reliance on machine learning and predictive analytics for real-time detection.
- Quantum-Safe Cryptography: Preparing defenses for the era of quantum computing.
- Autonomous Operations: Security systems that adapt automatically to neutralize threats.
Our Labs division is already investing in these innovations, from explainable AI to secure hardware and molecular data storage. By choosing Zentara today, enterprises future-proof themselves for tomorrow’s threats.
Conclusion: Why Partnering with Zentara Delivers Security Without Compromise
Cyber threats are no longer a matter of if but when. Enterprises cannot afford the cost, complexity, and risks of managing security alone. SOC as a Service provides a cost-effective, scalable, and expert-driven solution that ensures protection 24/7.
Our Managed SOC combines advanced technology, certified analysts, and relentless innovation to deliver defense-grade protection trusted worldwide. From compliance support to proactive threat hunting, our service offers peace of mind and strategic value.
Security is not just part of what we do—it is our foundation. It is our promise. And with Zentara, it is your advantage.