Mobile applications now handle banking transactions, healthcare data, enterprise credentials, and personal identities. For attackers, that makes them high-value targets.
Yet many organizations still treat mobile app security testing as a release checkbox rather than a continuous security function.
From a Red Team perspective, the same patterns appear repeatedly. Not exotic zero-days. Not cinematic exploits. Just preventable weaknesses that remain untested or misunderstood.
Here are the mobile app vulnerabilities attackers exploit most, and what proper mobile app security testing should uncover.
1. Insecure Data Storage
Insecure local data storage remains one of the most common weaknesses in mobile apps. Sensitive data often ends up in plaintext within app directories or cached files, or in unencrypted shared preferences on Android devices.
Attackers with device access (through malware, jailbreaking, or lost devices) can extract authentication tokens, user data, or API credentials. Effective testing examines where data is stored, how it’s encrypted, and whether tokens expire properly. If sensitive data can be recovered without breaking encryption, the app fails at the most basic level.
2. Broken Authentication and Session Management
Authentication flaws are among the most profitable attack vectors. In real-world engagements, attackers often reuse exposed tokens or intercept poorly protected session data rather than “hack” authentication directly.
Common issues include weak session token handling, predictable identifiers, and insecure password reset flows. Testing must simulate token replay, session hijacking, and MFA bypass attempts. Security controls must hold under adversarial pressure—not just normal user flow.
3. Insecure API Communication
Mobile apps rely heavily on backend APIs, and when those APIs are poorly protected, the app becomes a convenient entry point. Attackers often bypass the mobile interface entirely and interact directly with backend endpoints.
Testing should include API enumeration, authorization checks, and certificate pinning validation. If backend security assumes the mobile app cannot be manipulated, that assumption will eventually fail.
4. Insufficient Certificate Validation and MITM Exposure
Many apps rely on HTTPS but fail to validate certificates properly. Without certificate pinning or correct TLS configuration, attackers can intercept traffic via rogue Wi-Fi networks and manipulate API responses.
During testing, security teams perform man-in-the-middle (MITM) attacks to verify whether traffic can be intercepted or modified. If encrypted traffic can be inspected without resistance, the application’s trust model is broken.
5. Hardcoded Secrets and Reverse Engineering Risks
Attackers routinely decompile mobile apps to analyze their code. If secrets such as API keys, encryption keys, or internal endpoints are embedded directly in the application, they will be discovered.
Testing should include static code analysis, reverse engineering attempts, and binary inspection. Security through obscurity is not security. Assume your app will be reverse engineered.
6. Broken Authorization (IDOR and Privilege Escalation)
Insecure Direct Object References (IDOR) remain common in mobile ecosystems. Predictable or insufficiently validated identifiers allow attackers to access other users’ data or modify transactions.
Authorization testing must validate role-based access controls and object ownership enforcement. Authentication verifies identity; authorization enforces boundaries. Confusing the two leads to breach conditions.
7. Insecure Third-Party SDKs
Modern mobile apps integrate analytics, payment, and social login SDKs, each introducing additional attack surface. Outdated or misconfigured SDKs can leak data or enable injection vulnerabilities.
Testing should inventory third-party components and assess known vulnerabilities, especially in high-risk environments like fintech and healthcare.
Why Traditional Testing Is Not Enough
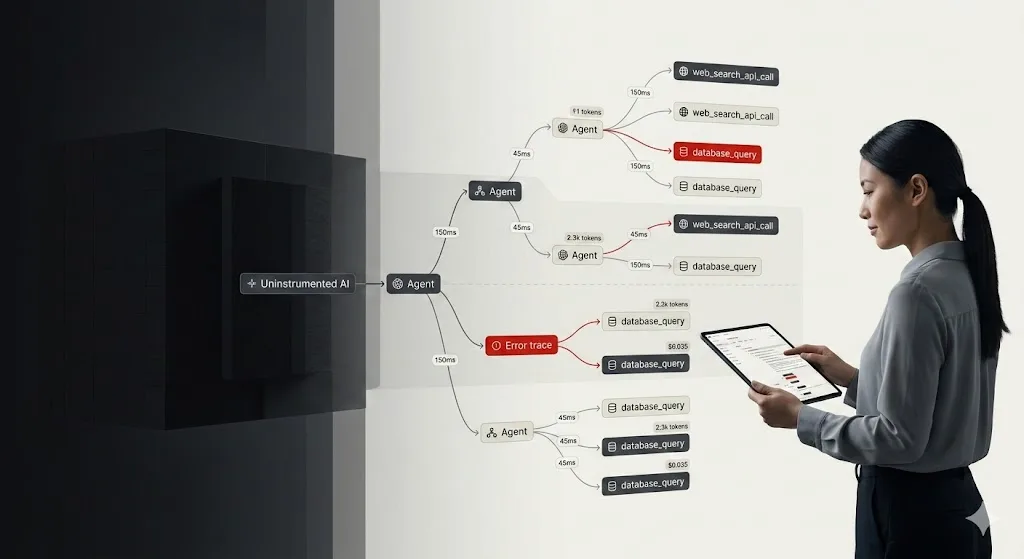
Automated scanning tools are useful but limited. They cannot validate business logic flaws, simulate realistic attacker workflows, or identify chained vulnerabilities.
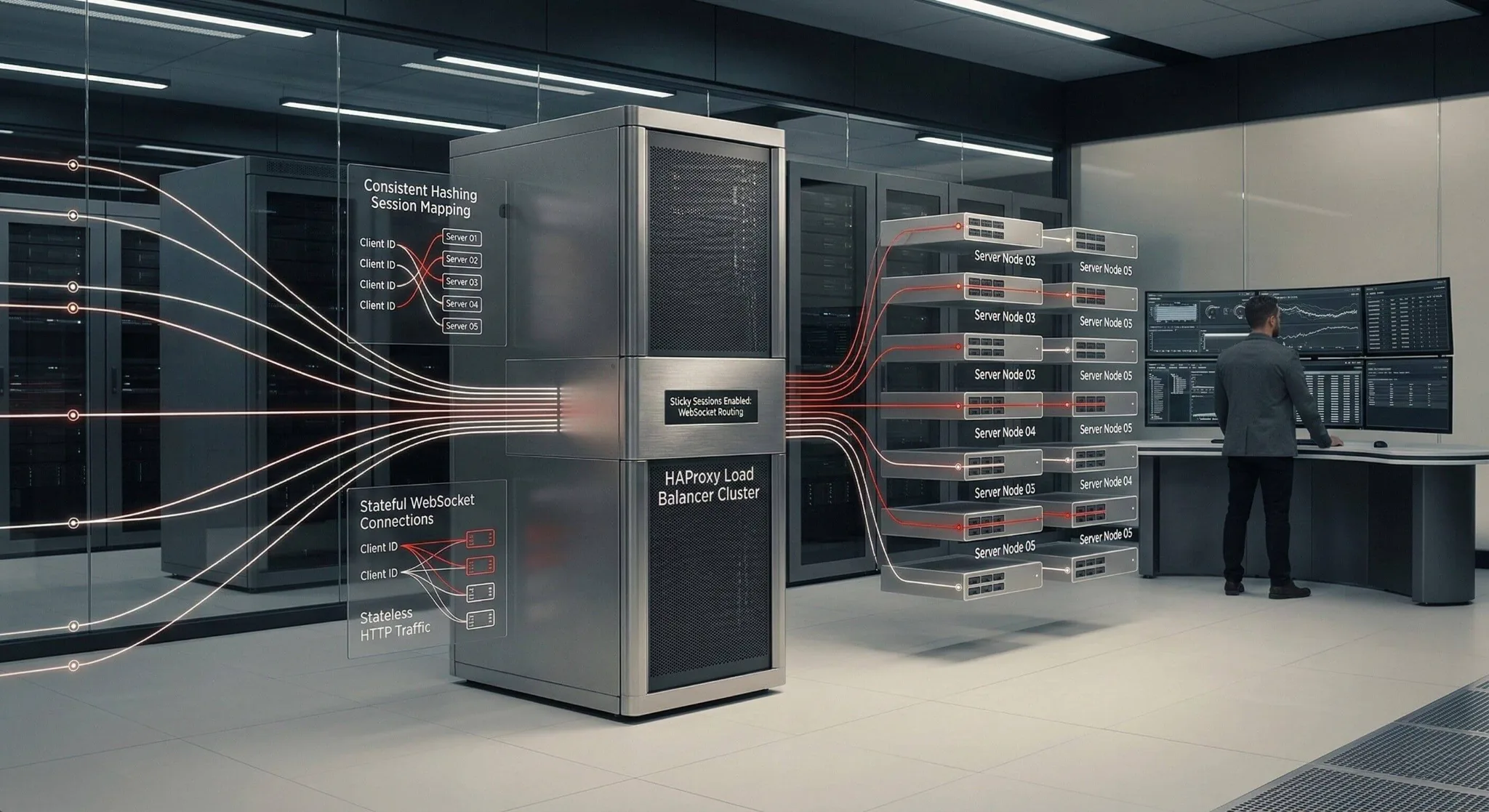
Effective mobile app security testing combines static and dynamic analysis, manual penetration testing, API testing, and business logic evaluation. Attackers think in chains, and security testing must do the same.
Mobile App Security in High-Growth Sectors
In Southeast Asia, fintech, e-commerce, and digital banking apps are expanding rapidly. With growth comes exposure: larger user bases, more APIs, and increased third-party integrations.
Without continuous mobile app penetration testing, vulnerabilities scale with user growth. Mobile security must evolve at the same speed as product development.
Test Like an Attacker
Mobile applications are not secure because they are encrypted. They are secure when sensitive data is protected at rest and in transit, authentication and authorization are resilient, APIs enforce strict controls, and secrets are not embedded in client code.
Mobile app and cloud security testing should be continuous, adversarial, and aligned with real-world attack techniques.
Strengthen Your Mobile App Security Testing With Zentara
Zentara’s Red Team conducts in-depth mobile app security testing, including API validation, reverse engineering analysis, and real-world exploitation scenarios.
If your application handles sensitive data or financial transactions, contact our team to assess your mobile security posture before attackers do.