In 2026, the aftermath of a cyberattack is no longer a “black box” of lost data. As organisations transition to hyper-automated and cloud-native environments, the trail of digital forensic evidence left behind has become more complex but also more detailed than ever before.
Whether you are a business owner facing a ransomware demand or an IT manager tasked with a post-mortem, understanding what can be salvaged is the first step toward recovery. This guide breaks down the reality of modern evidence recovery, from the volatile memory of a local server to the ephemeral logs of a global cloud network.
What is Digital Forensic Evidence?
In a technical sense, digital forensic evidence refers to any information stored or transmitted in binary form that can be used to reconstruct a cyber incident. Unlike physical evidence, digital artefacts are exceptionally fragile. A single reboot or a poorly timed antivirus scan can overwrite the very data needed to identify “Patient Zero.”
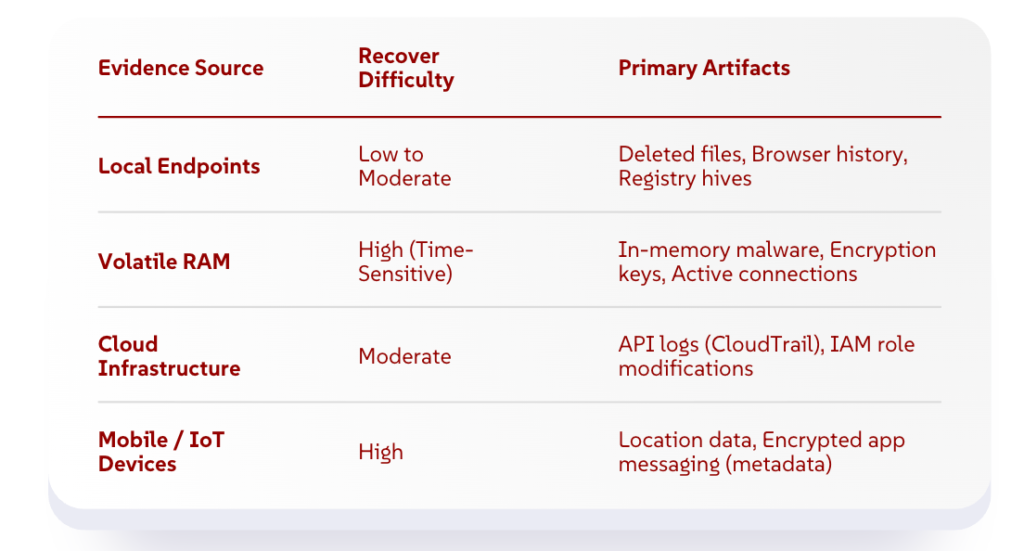
By 2026, the definition of digital evidence has expanded beyond hard drives. It now encompasses a “living” ecosystem of telemetry, including:
- Persistent Data: Files, registry keys, and system logs stored on physical or virtual disks.
- Volatile Data: Information held in Random Access Memory (RAM) that disappears when power is lost.
- Metadata: The “data about data”: timestamps, geolocation, and author identity, that often proves more valuable than the content itself.
Evidence Recovery Potential by Source
Incident Response: The “Golden Hour” of Evidence
The success of any investigation depends heavily on the speed and quality of your incident response. In forensic circles, we refer to the first 60 minutes after detection as the “Golden Hour.” During this window, the most critical pieces of digital forensic evidence are still resident in the system’s volatile memory.
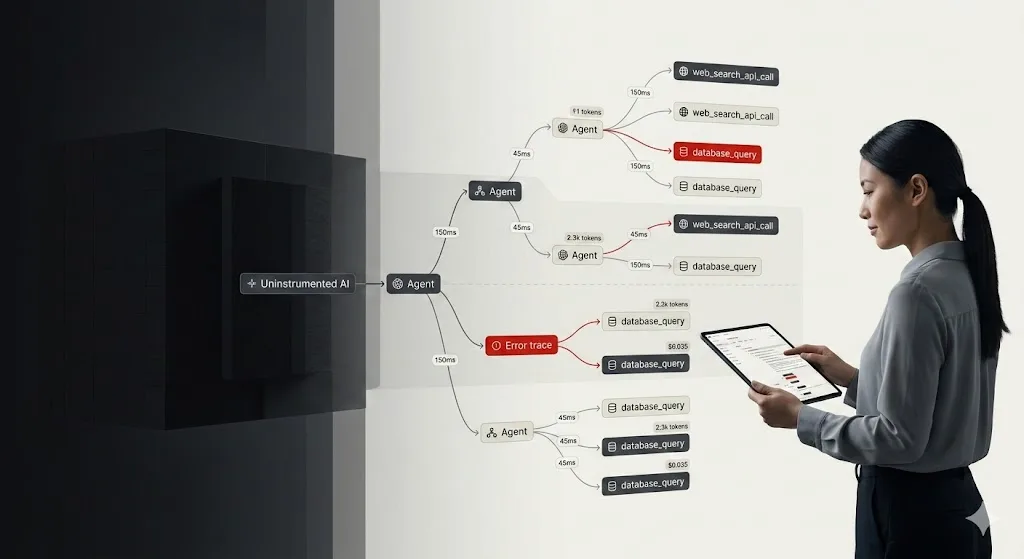
Modern attackers often use “living-off-the-land” (LotL) techniques, where they use legitimate system tools to carry out their strike without ever writing a file to the disk. If your incident response plan involves immediately pulling the plug or rebooting the server, you effectively “wipe the fingerprints” from the crime scene. Professional responders now prioritise “Live Forensics,” capturing a snapshot of the RAM and active network connections before the system is isolated.
Note: For a standardised framework on handling these early stages, the SANS Institute’s Incident Handling Guide provides a roadmap for preserving data integrity during a crisis.
Cloud Forensics: Recovering Evidence in a Borderless World
As enterprises shift to multi-cloud architectures, the focus of investigations has moved from physical hardware to virtualised environments. Cloud forensics is now a specialised discipline required for almost every major breach.
In the cloud, you don’t “seize” a hard drive. Instead, investigators rely on provider-native logs and snapshots. Key recoverables in a cloud environment include:
- Management Plane Logs: Every time an admin (or a hacker) changes a security group or creates a new user, a log is generated.
- Ephemeral Artefacts: In containerised environments (like Kubernetes), logs must be offloaded to a persistent store instantly, or they vanish when the container scales down.
- Object Storage Metadata: Even if a file is deleted from an S3 bucket or Azure Blob, the metadata often reveals who deleted it and from which IP address.
The challenge in cloud forensics is often jurisdictional. Data may be stored across three different continents, making legal access as complex as the technical recovery. Organisations should align their logging policies with the NIST Cloud Computing Forensic Reference Architecture to ensure they are “forensic-ready” before an incident occurs.
What Evidence Can Actually Be Recovered?
When clients ask, “What can you find?”, the answer is often surprising. Even when an attacker attempts to cover their tracks, modern digital forensic evidence recovery techniques can surface the following:
1. Deleted Files and Data Carving
Even if a file is “permanently” deleted, the underlying data often remains on the disk until it is overwritten by new information. Forensic tools use “data carving” to identify file headers and footers, piecing together fragments of documents, images, or code that the attacker thought were gone.
2. Lateral Movement Traces
Hackers rarely stay on the first computer they compromise. They move through the network looking for “crown jewels.” Investigators can recover RDP (Remote Desktop Protocol) cache, SSH logs, and Kerberos tickets to map exactly how the intruder navigated your internal systems.
3. “Pattern of Life” Artefacts
Systems maintain a record of user behavior. Prefetch files, Shimcache, and Shellbags tell a story: “At 2:00 PM, the user opened a web browser; at 2:05 PM, they downloaded a zip file; at 2:10 PM, they ran a PowerShell script.” This timeline is the backbone of any legal case involving digital forensic evidence.
4. Communication Metadata
While end-to-end encryption in apps like Teams or Slack makes reading content difficult, it does not hide the metadata. We can often recover the “who, when, and where” of communications, which is frequently enough to prove intent or collusion.
Ensuring Your Evidence is Admissible
Collecting digital forensic evidence is only half the battle; the other half is ensuring it holds up in court or for an insurance claim. This requires a strict “Chain of Custody.” This is a chronological paper trail that documents who had access to the evidence from the moment it was collected to the moment it was presented.
If a single link in this chain is broken, for example, if an IT staff member logs into a compromised machine using an admin account, the defence can argue that the evidence was tampered with, potentially rendering the entire investigation useless.
Preparing for the Unpredictable
By 2026, the question is no longer if you will need to recover data, but how prepared you are to do so. The depth of digital forensic evidence available today is staggering, but its value is entirely dependent on your organisation’s readiness.
By integrating forensic preservation into your regular security posture, you ensure that when an incident occurs, you aren’t just reacting to a crisis. You are capturing the truth.
To ensure your critical data is preserved and your organisation is protected, partner with the experts at Zentara to build a resilient, forensic-ready security posture that stands up to modern threats.