The digital landscape is defined by a paradox: organisations are more “compliant” than ever, yet sophisticated breaches continue to make headlines. This disconnect often stems from a fundamental misunderstanding of two critical pillars of defence. When leadership asks, “Are we secure?”, the answer depends entirely on whether you are looking through the lens of a cybersecurity audit or a cybersecurity risk assessment.
While these terms are often used interchangeably in boardrooms, they serve two distinct masters. One is designed to satisfy regulators and insurers; the other is designed to keep hackers out of your core infrastructure. To build a resilient organisation, you must understand how to balance the binary “Pass/Fail” nature of an audit with the nuanced, threat-driven reality of an assessment.
What is a Cyber Security Audit? (The Compliance Pillar)
A cyber security audit is a formal, point-in-time examination of your organisation’s adherence to a specific set of established standards. Think of it as a financial audit for your data. It is typically conducted by an independent third party to ensure that “what you say you are doing” matches “what you are actually doing.”
In the context of 2026 regulatory demands, an audit is the primary tool for compliance validation. Whether you are aiming for ISO 27001 certification, SOC 2 Type II readiness, or meeting the latest SEC disclosure requirements, the audit is your proof of governance.
The Scope of an Audit
Audits are inherently rigid. An auditor arrives with a checklist derived from a framework (like NIST or CIS) and looks for evidence of controls.
- Documentation Review: Are your policies signed and updated?
- Access Control Logs: Can you prove that terminated employees were offboarded within 24 hours?
- Encryption Standards: Is data at rest encrypted using approved algorithms?
The result of a cybersecurity audit is a report of non-conformities. It tells you where you are breaking the rules, but it doesn’t necessarily tell you if those rules are enough to stop a modern AI-driven threat actor.
What is a Cyber Security Risk Assessment? (The Safety Pillar)
If an audit is a snapshot of a moment in time, a cybersecurity risk assessment is a stress test of your entire ecosystem. The goal here isn’t to check a box; it’s to identify, prioritise, and manage vulnerabilities before they can be exploited.
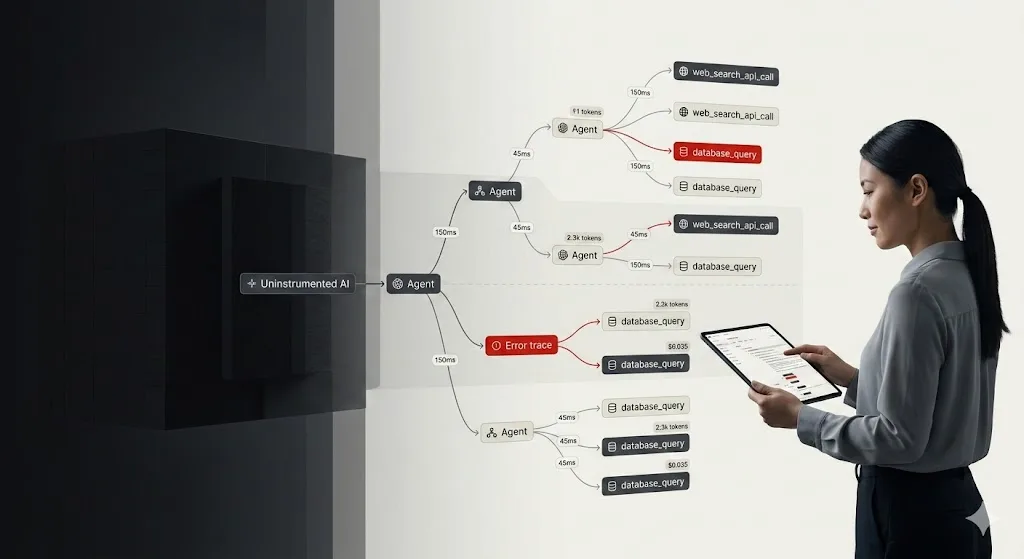
This process is the heartbeat of cybersecurity risk mitigation. Instead of asking “Do we have a firewall?”, an assessment asks “Given our specific business model and current threat intelligence, how could an attacker bypass our firewall to reach our customer database?”
Key Components of an Assessment
- Threat Modeling: Identifying specific adversaries (e.g., state-sponsored actors vs. opportunistic ransomware groups) likely to target your industry.
- Vulnerability Analysis: Scanning and testing assets to find technical weaknesses.
- Impact Analysis: Determining the “Blast Radius.” If this specific server goes down, does it cost the company $10,000 per hour or $1,000,000?
A cybersecurity risk assessment provides a roadmap for resource allocation. It tells you where your “Safety” is thin, regardless of what the compliance paperwork says.
The Critical Difference: Compliance vs. Safety
The most dangerous mistake a CISO can make is assuming that a clean audit equates to a safe environment. This “Compliance Trap” has led to numerous high-profile failures.
Why Compliance Isn’t Safety
Compliance frameworks are often reactive. They are built on the lessons learned from yesterday’s breaches. An audit might confirm you have an antivirus installed (Compliance), but an assessment might reveal that your specific antivirus configuration is easily bypassed by modern fileless malware (Safety).
Why Safety Isn’t Always Compliant
Conversely, you could have the most secure, air-gapped network in the world, but if you haven’t documented the processes or performed the required quarterly reviews, you will fail a cybersecurity audit. For many organisations, failing an audit means losing a major contract or facing massive regulatory fines, even if no data was ever at risk.
Measuring Security Control Effectiveness
To bridge the gap between these two worlds, 2026 enterprises are focusing on security control effectiveness. This metric looks at whether a control (like Multi-Factor Authentication) is both meeting the compliance requirement and actually stopping unauthorised access.
According to the Verizon 2025 Data Breach Investigations Report, misconfigurations and human error remain the leading causes of breaches, despite many of those organisations holding valid security certifications. This highlights the need for continuous testing, moving away from the “once-a-year” audit model toward a philosophy of continuous security validation.
Choosing Between a Cyber Security Audit and Cyber Security Risk Assessment
Deciding where to spend your budget depends on your current business stage and external pressures.
When to Prioritise a Cyber Security Audit
- Contractual Obligations: A new enterprise client requires a SOC 2 report before signing.
- Regulatory Deadlines: You operate in a highly regulated sector like Finance (NYDFS) or Healthcare (HIPAA).
- Insurance Renewals: Your cyber insurance provider requires an independent audit to set your premiums.
When to Prioritise a Cyber Security Risk Assessment
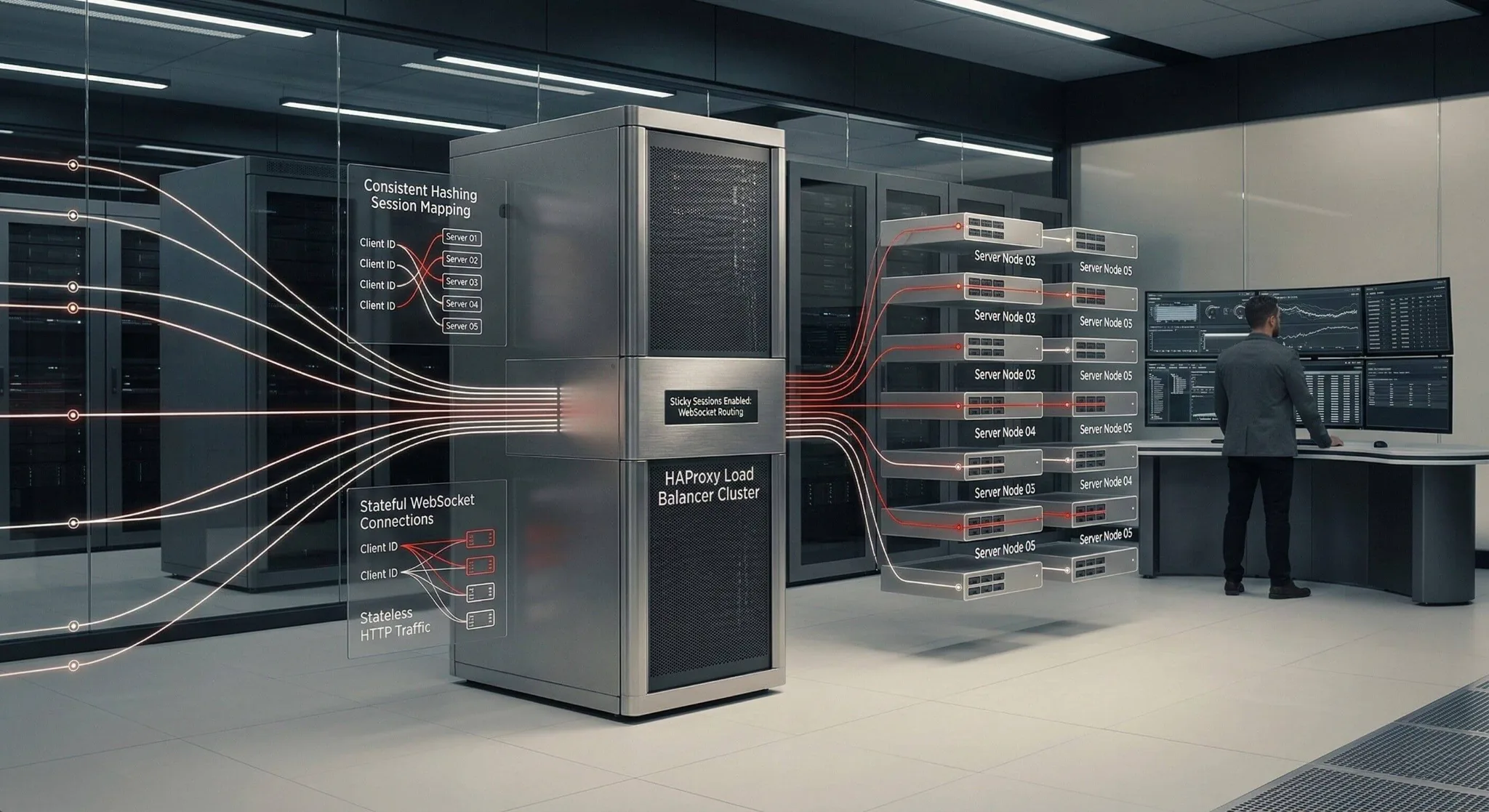
- Infrastructure Changes: You are migrating from on-premise servers to a serverless cloud architecture.
- Mergers & Acquisitions: You need to know the hidden “technical debt” and security holes in a company you are about to buy.
- Budget Planning: You need to justify a $500k investment in a new SOC and need to prove exactly which risks it will mitigate.
The 2026 Strategy: The Integrated Approach
In a mature security posture, the cybersecurity audit and cybersecurity risk assessment function as a feedback loop. The assessment identifies a new risk (e.g., a vulnerability in a new API); a control is implemented to mitigate that risk; and the audit later verifies that the control is being maintained consistently across the organisation.
By integrating these two, you achieve “Audit-Ready Security”, a state where you are inherently safe because of your risk management, and naturally compliant because your safety measures are well-documented.
Summary Checklist for Leadership
- Audit: Focuses on past performance and current rules. (Are we following the law?)
- Assessment: Focuses on future threats and potential impact. (Are we going to get hacked?)
Understanding the distinction between a cybersecurity audit and a cybersecurity risk assessment is the difference between surviving a regulatory inspection and surviving a targeted cyberattack. While compliance provides the necessary foundation for trust in the marketplace, it is the proactive nature of risk assessment that ensures your operational longevity. In 2026, you cannot afford to choose one over the other; you must master the intersection of both.
To ensure your organisation meets every compliance benchmark while staying ahead of evolving threats, partner with the specialists at Zentara for an integrated security strategy that delivers both peace of mind and ironclad protection.